The Menace of GootLoader and SocGholish Malware Strains
In January and February 2023, six different law firms were attacked by two distinct threat campaigns, which unleashed GootLoader and FakeUpdates (aka SocGholish) malware strains.
GootLoader: The Capable First-Stage Downloader
GootLoader, active since late 2020, can deliver a broad range of secondary payloads, such as Cobalt Strike and ransomware.
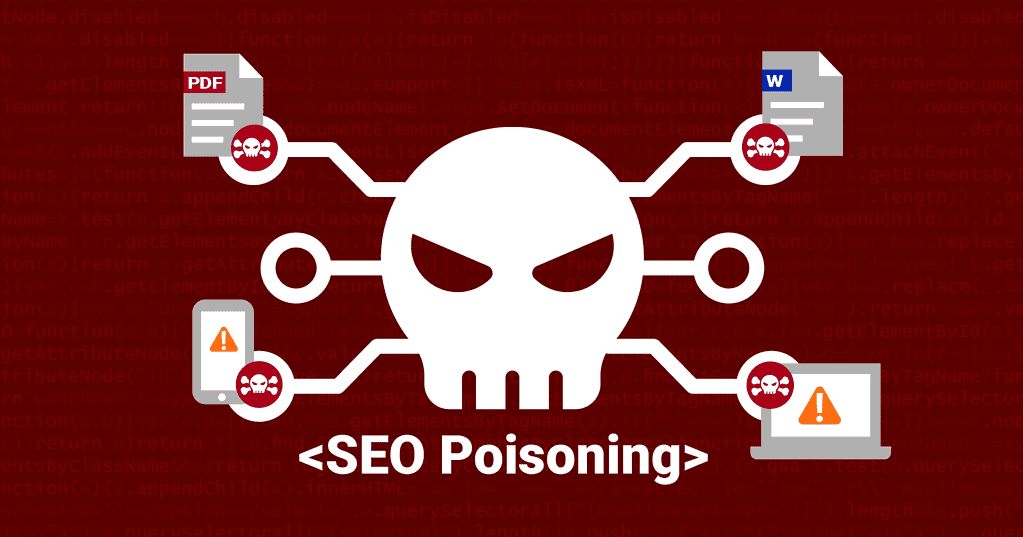
The malware utilizes search engine optimization (SEO) poisoning to redirect victims searching for business-related documents toward drive-by download sites, which drop the JavaScript malware.
Compromised Websites: The Gateway to Malware
eSentire, a cybersecurity firm, noted that the threat actors behind the campaign compromised legitimate but vulnerable WordPress websites and added new blog posts without the owners’ knowledge.
The Role of SocGholish in Law Firm Attacks
SocGholish, another downloader, can drop more executables in addition to GootLoader. It has also been used in attacks targeting law firm employees and business professionals.
Noteworthy Infection Chain and Attack Tactics
The attacks using GootLoader and SocGholish are notable for their lack of ransomware deployment, favoring hands-on activity. This indicates that the scope of the attacks may have diversified to include espionage operations.
Browser-Based Attacks: Competing with Email
The shift from email to browser-based attacks as the primary infection vector has been a gradual but significant change from 2021 to 2023. This shift has been due to malware strains such as GootLoader, SocGholish, SolarMarker, and campaigns using Google Ads to appear in the top search results.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.






