
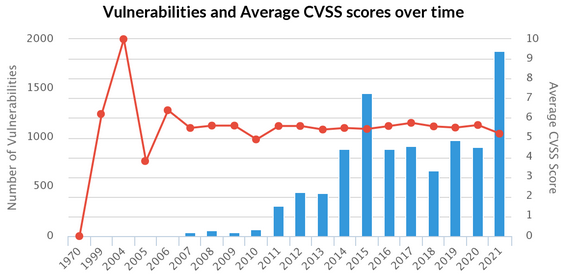
Riskbased Security researchers revealed a huge increase of WordPress vulnerabilities in 2021 in their latest research.
10,359 vulnerabilities were reported to affect third-party WordPress plugins at the end of 2021. Of those, 2,240 vulnerabilities were disclosed last year, which is a 142% increase compared to 2020.
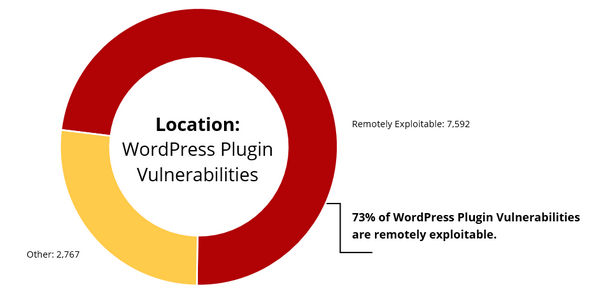
Most Plugin Vulnerabilities are Exploitable
What is most alarming is that 77% of WordPress plugin vulnerabilities have known public exploits.
- 7,592 WordPress vulnerabilities are remotely exploitable
- 7,993 WordPress vulnerabilities have a public exploit
- 4,797 WordPress vulnerabilities have a public exploit, but no CVE ID
Prioritize Your Patching
Riskbased Security suggests that your organization should prioritize patching of vulnerabilities based on their exploitability. Do less “mass patching” and focus on targeted, intelligent risk-based patching.
Start with vulnerabilities that are remotely exploitable, have a public exploit, and have a known solution. And if WordPress plugin issues affect important assets, these vulnerabilities should be triaged first.
This risk-based approach will prove to be more effective than traditional Vulnerability Management models based on severity.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.






