The Origins of BlackLotus
In October of the previous year, a nefarious bootkit named BlackLotus surfaced on underground hacker forums. Crafted exclusively for Windows systems, this malicious software boasted capabilities typically associated with advanced persistent threats (APTs).
Its ominous features included the ability to bypass secure boot and user access control (UAC), disable security software, and dismantle defensive mechanisms on compromised computers.
Initially offered on hacker forums for a mere $5,000, BlackLotus provided threat actors, regardless of their skill level, access to a potent malware often associated with state-sponsored hacking operations.
Alarming as it was, the source code remained concealed, forcing clients to pay an additional $200 if they desired any modifications to the bootkit.
Exposing the Bootkit: A Dangerous Revelation
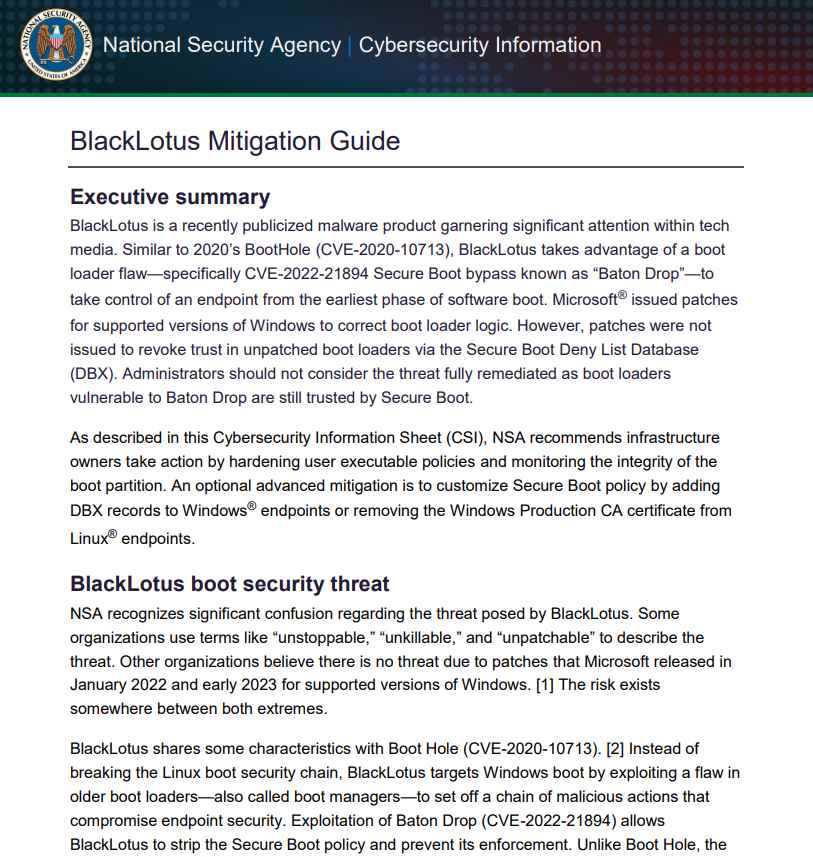
Microsoft responded to the growing threat by releasing resources in April, aiming to aid threat hunters in detecting BlackLotus infections. In June, the National Security Agency (NSA) published guidelines to help organizations fortify their defenses against this insidious threat.
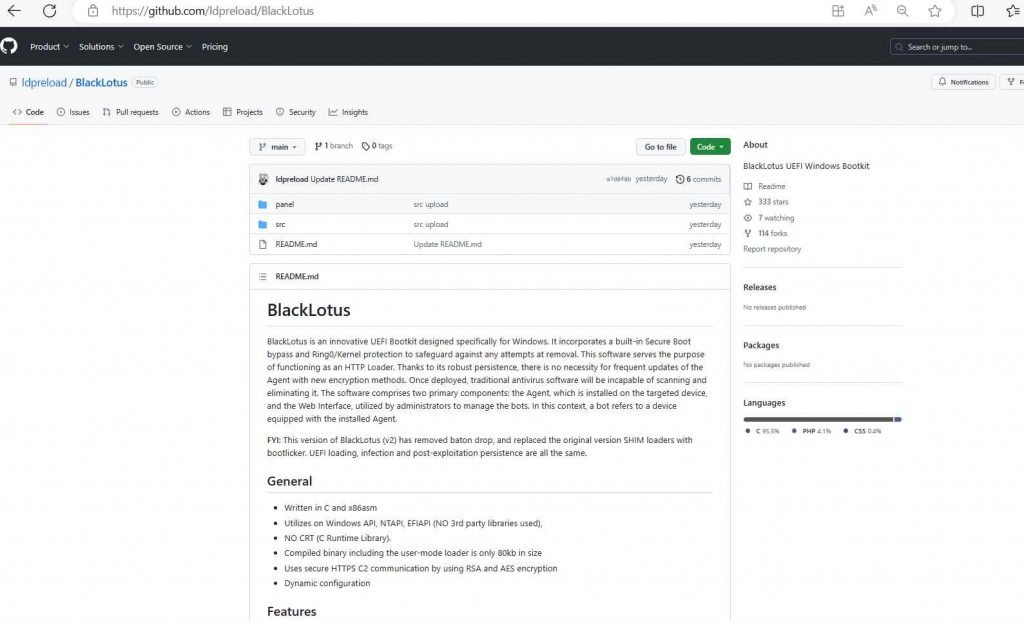
Recently, the original source code of the BlackLotus UEFI bootkit, albeit with some modifications, has been publicly disclosed on GitHub. Notably, the ‘Baton Drop’ exploit, targeting CVE-2022-21894, has been removed from the released source code. However, the bootkit still retains the majority of its original code while incorporating the bootlicker UEFI firmware rootkit.
Vulnerabilities Unleashed: The Risks of Public Source Code
The public availability of the bootkit’s source code poses a significant danger, as it can be combined with newly discovered vulnerabilities. This alarming prospect opens up previously unknown entry points for potential attacks.
BlackLotus successfully exploited the system despite CVE-2022-21894 being patched in the previous year. This occurred due to the vulnerable binaries not being added to the UEFI revocation list, highlighting how patched vulnerabilities can still have long-term repercussions throughout the industry’s supply chain.
With the leak of the source code, threat actors now have the means to merge the bootkit with bootloader vulnerabilities, both known and yet to be discovered. The once cutting-edge techniques employed by the bootkit are no longer exclusive to its arsenal.
Stay Vigilant: Safeguarding Against the BlackLotus UEFI Bootkit
To protect your computers against the BlackLotus UEFI bootkit attack, it is imperative to follow the extensive mitigation guidance issued by the NSA a month ago. As the source code becomes readily accessible, skilled malware creators may develop even more formidable variations capable of evading current and future countermeasures.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.