
Know what GDPR is and how it can protect and give you more control over your personal data. You have rights over your data, learn what those are and how you can use them. So here is a simple summary of GDPR.
WHAT IS GDPR
GDPR or General Data Protection Regulation is the world’s strongest set of data protection rules which enhance how people can access information about them and place limits on what organizations can do with personal data.
The regulation exists as a framework for laws across the continent and replaced the previous 1995 data protection directive. The GDPR’s final form came about after more than four years of discussion and negotiations – it was adopted by both the European Parliament and European Council in April 2016.
GDPR came into force on May 25, 2018. Countries within Europe were given the ability to make their own small changes to suit their own needs. Within the UK this flexibility led to the creation of the Data Protection Act (2018), which superseded the previous 1998 Data Protection Act.
WHAT ARE PERSONAL DATA
The GDPR defines personal data as:
“‘personal data’ means any information relating to an identified or identifiable natural person (‘data subject’); an identifiable natural person is one who can be identified, directly or indirectly, in particular by reference to an identifier such as a name, an identification number, location data, an online identifier or to one or more factors specific to the physical, physiological, genetic, mental, the economic, cultural or social identity of that natural person”.
This means personal data has to be information that relates to an individual. That individual must be identified or identifiable either directly or indirectly from one or more identifiers or from factors specific to the individual.
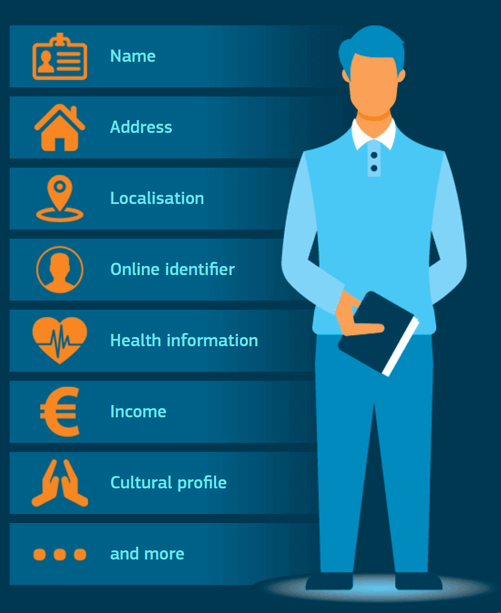
Personal data includes an identifier like:
- your name
- an identification number, for example, your National Insurance or passport number
- your location data, for example, your home address or mobile phone GPS data
- an online identifier, for example, your IP or email address.
SENSITIVE PERSONAL DATA
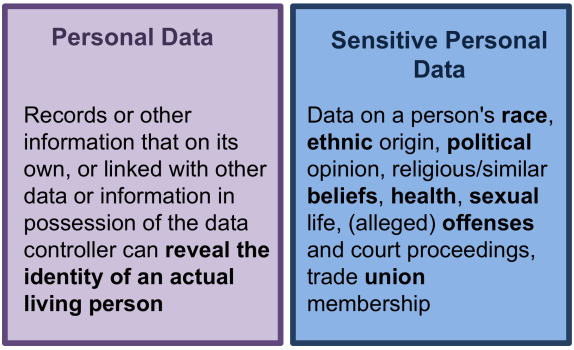
Sensitive personal data is also covered in GDPR as a special category of personal data. The special categories specifically include:
- genetic data relating to the inherited or acquired genetic characteristics which give unique information about a person’s physiology or the health of that natural person
- biometric data for the purpose of uniquely identifying a natural person, including facial images and fingerprints
- data concerning health which reveals information about your health status, including both physical and mental health and the provision of health care services
- racial or ethnic origin
- political opinions
- religious or philosophical beliefs
- trade union membership
- sex life or sexual orientation.
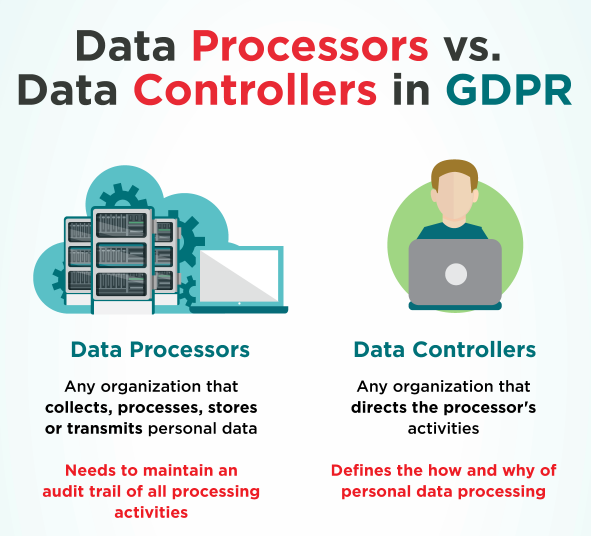
CONTROLLERS AND PROCESSORS
Controllers and processors are two different types of organizations that GDPR applies to-namely, those that “control” personal data, and those that “process” it. A data processor in GDPR is defined as any organization that collects, processes, stores or transmits personal data of EU data subjects. A data controller is an organization that directs the processor’s activities.
KNOW YOUR RIGHTS BASED ON GDPR

Your rights cannot be missing from a summary on GDPR, no matter how simple it is 🙂
- The right to be informed
- The right of access
- The right of rectification
- The right to erasure
- The right to restrict processing
- The right to data portability
- The right to object
- The right to automated decision-making and profiling
GDPR KEY PRINCIPLES
At the heart of GDPR are seven key principles that have been designed to guide how personal data can be handled.

Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.






