
The importance of the DNS service for the internet is widely understood. Most applications today rely on DNS to locate resources across the internet in order to operate. This presents challenges for us security professionals as DNS relates to overall security in several ways, some of which may not be understood correctly.
You have to understand DNS to properly apply the necessary security controls to it.
There are several types of attacks that a hacker can use against your organization’s DNS servers. As a security professional, you should know the differences between the most common DNS attacks so that you know what types of controls you need to apply to defend against them and identify the attack instead of treating its symptoms as performance issues.
Types of Attacks
- Domain Hijacking
- DNS flood attack
- Distributed Reflection Denial of Service (DRDoS)
- Cache poisoning
- DNS Tunneling
- Pseudo Random Sub Domain DDoS (PRSD) Attack
- NXDOMAIN attack
- Phantom domain attack
Domain Hijacking

This attack involves redirecting users to a different destination. This attack can happen after compromising the DNS server used by the client and changing the associated DNS records or by changing the local host file to point a domain name to a malicious IP address controlled by the attacker. Sometimes, we use the term DNS Hijacking and DNS Spoofing interchangeably.
DNS Flood Attack

These attacks attempt to exhaust the DNS server resources (RAM or CPU) with a flood of UDP requests. The attack is usually carried out through several compromised machines under a botnet network.
DRDoS Attack

The DRDoS attack is similar to a DoS attack. The difference is that the attacker spoofs the target IP address when sending DNS requests so that the replies will be sent to the victim causing a DoS to the victim services.
Cache Poisoning
Cache poisoning is a more specific type of attack targeting caching name servers in an attempt to control the answers stored in the DNS cache. There are different methods to carry out this attack, but they typically involve flooding the recursive server with forged DNS responses, changing the query ID in each response hoping to guess the right ID at just the right time.
This attack is very difficult to detect, and very difficult to guard against unless DNSSEC is fully deployed.

DNS Tunneling
DNS Tunneling has been around for almost 20 years!
Attackers tunnel protocols like SSH or HTTP within DNS to secretly transmit data and fully remote control compromised internal hosts.
For example, a client sends a query for an A record where the data is base64 encoded in the hostname (<base64_encoded_data>.evilsite.com)
you can encode/decode from and to base64 from this site. (Try decoding “cGFzc3dvcmQK” as an example.) Of course, you can use non-encoded DNS names for the requests.
In the DNS tunneling scenario, the attacker registers a domain name, e.g. evilsite.com. Then points its nameserver records towards the server where the DNS tunneling server program is running. The server acts as an authoritative name server for that domain name and its sub-domain to facilitate server-side tunneling and decapsulating the payload data by running the DNS tunnel server daemon on the server.
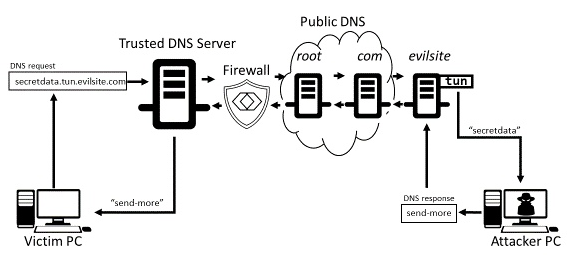
You can send all kinds of data through this tunnel. It will be VERY slow but effective.
Very few system/network administrators or security teams have the knowledge, time or resources to monitor such requests for malicious activity.
Pseudo Random Sub Domain DDoS (PRSD) Attack
During this attack, the attacker sends queries to open proxies around the world for non-existent subdomains of your domain (e.g. akfdhafhdsajh.yourcompany.com)
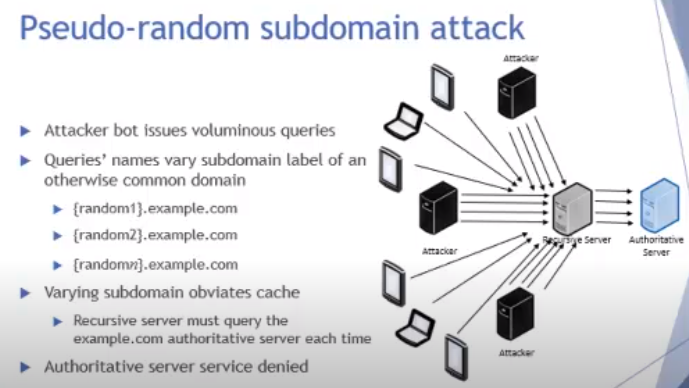
These queries are forwarded to DNS resolvers at the upstream ISP. Although the attacks are intended to take down the authoritative servers for these legitimate domains, they have the side effect of dramatically increasing the load on ISP’s DNS resolvers to the point that they, too, can become overloaded and either slow down or crash.
NXDOMAIN Attack
The NXDOMAIN Attack is another Denial-of-Service DNS attack. In this situation, the attacker floods the DNS server with false queries to resolve a non-existent domain name. This results in choking up the cache with NXDOMAIN results and hence slows down the response of the legitimate requests.
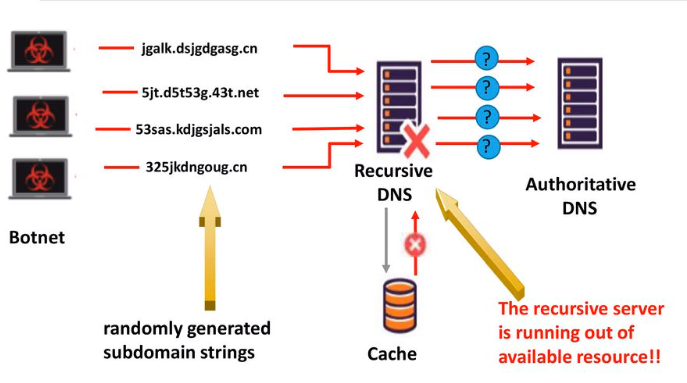
Most often the DNS server administrators confuse these with performance issues when actually their DNS servers are under NXDOMAIN attack.
Phantom Domain Attack
The Phantom Domain Attack is similar to the NXDOMAIN attack.
The attacker sets up a bunch of ‘phantom’ domain servers which either respond to requests very slowly or not at all. The resolver is then hit with a flood of requests to these domains and the resolver gets tied up waiting for responses, leading to slow performance and denial-of-service.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.





