Trigona ransomware is a newly discovered malware that poses a serious threat to Windows users. The Unit42 research team at Palo Alto Networks recently detected this ransomware and found it to use uncommon techniques for attacking Windows. This article provides an overview of the Trigona ransomware, its attack methods, and the potential risks it poses to users.
Trigona Ransomware Overview
The Trigona ransomware was first discovered in October 2022, and it was particularly active in December 2022. It has affected nearly 15 organizations in various industries such as Manufacturing, Finance, Construction, Marketing, and High Technology. As of January and February of 2023, four ransom notes of Trigona were found, with two each month.
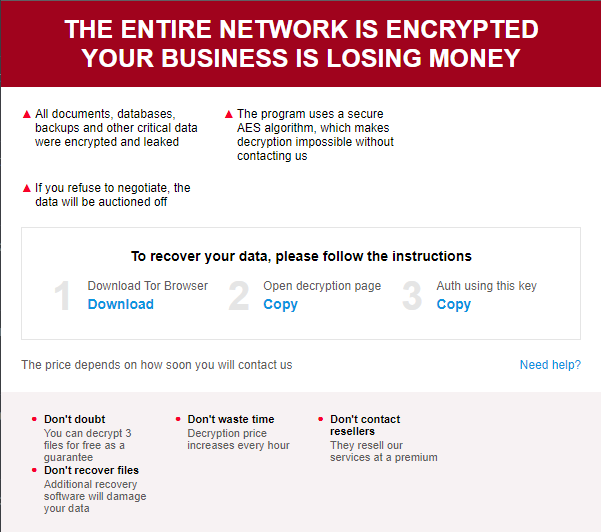
Unlike other ransomware notes, Trigona notes were not plain-text files.
Instead, they are an HTML application with embedded JS. It also contains CIDs (Computer IDs) and VIDs (Victim IDs).
Attack Methods of Trigona Ransomware
According to a security researcher’s tweet, the creators of Trigona ransomware first obtain initial access to a victim’s environment by conducting active reconnaissance, transferring malware through remote monitoring and management (RMM), and creating and deploying user accounts.
As per reports, Trigona ransomware has a list of command lines and is supported by TDCP_rijndael (a Delphi AES library) for encrypting files. The extension of the affected files is with ._locked, and the ransom note has a filename and extension as how_to_decrypt.hta.
Further observation of the file showed some parameters containing the following information:
- CID and VID
- Email Address (Attacker)
- TOR URL for negotiation.
Trigona Ransomware Risks
Trigona ransomware is particularly dangerous because of its Mimikatz exploitation tool, which it uses for credential loading, dumping, manipulation, and injection before attempting to encrypt the files. A password-protected version of Mimikatz is used to extract sensitive information from a Windows operating system, such as passwords and authentication credentials. This tool allows Trigona ransomware to perform the following actions:
- Loading Credentials – Retrieves credentials from various locations, including Windows memory, the Local Security Authority Subsystem Service (LSASS) process, and the Windows registry.
- Dumping of Credentials – Extracts and dumps the credentials to the screen or a file, including usernames and passwords, hashes, and Kerberos tickets.
- Manipulation of Credentials – Allows users to change passwords, create new user accounts, and add people to groups using the leaked credentials.
- Injection of Credentials – Injects altered credentials into other processes, allowing the user to impersonate another user and access restricted resources.
Binaries supported by Trigona include:
- /full – Performs all functions of the ransomware. Encrypts both local and network files. Creates two registry keys for persistence, one for the ransomware binary and another for the ransom note.
- /!autorun – Skips creation of registry keys for persistence.
- /test_cid “test” – Overwrites default victim-generated CID and replaces it with “test” value.
- /test_vid “test” – Overwrites default VID and replaces it with “test” value.
- /p, /path “path” – Encrypts only files contained within the specified path.
- /!local – Does not encrypt local system files, only encrypts files on the local network.
- /!lan – Does not encrypt local network files, only encrypts files on the local system.
- /autorun_only “path” – Creates registry key for persistence only. Allows for an optional “path” to be provided to
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.