What is Passive Scanning?
Passive scanning is part of the passive reconnaissance phase of a penetration testing engagement. Passive recon is the attempt to gain information about your targets without actively engaging with the systems.
Nmap is a well known tool in a penetration tester’s arsenal. Although you will surely use it on one of your penetration testing engagements, it is not one of the tools you would want to use for a passive reconnaissance of your targets.
Nmap will probe your targets and this probing will create “noise” on the target’s network. If the target has monitoring systems, they will see you coming.
To retrieve similar information as nmap does, but by scanning your targets passively, you would want to use smap.
What is Smap?
Smap, is a tool based on nmap and built with Shodan.io. It uses shodan’s free API for port scanning.
The data you will get from a Smap scan are simply existing port data from shodan.io. If shodan hasn’t recently scanned your target and the target has some newly opened ports, you will not see them in your results.
Also, smap is limited in providing information on 1237 ports of your targets.
You may see the list of ports here. Those should be enough for your initial information gathering stage.
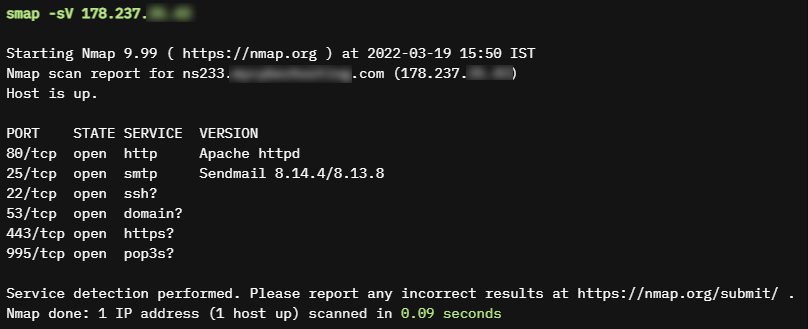
Smap is extremely fast but also has its limitations, the most serious of which is the out of date results which could be up to 7 days.
How to install and use smap
You can download a pre-built binary from here and use it right away.
OR
go install -v github.com/s0md3v/smap/cmd/smap@latest
Using smap is similar to using nmap. The difference is that the only options you can use are:
-p, -h, -o*, -iL
Summary
Smap is based on the infamous nmap.
It is a great tool which helps you gather information on your targets rapidly and passively. It will help you avoid detection in your early stages of a penetration testing engagement.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.





