
What is a MITM Attack
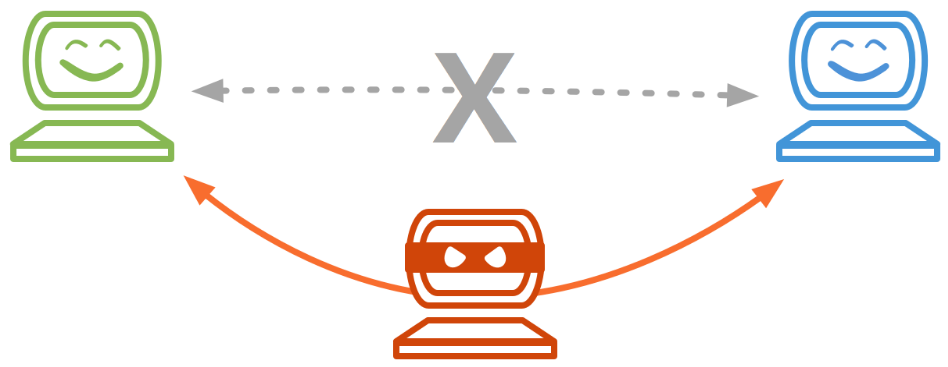
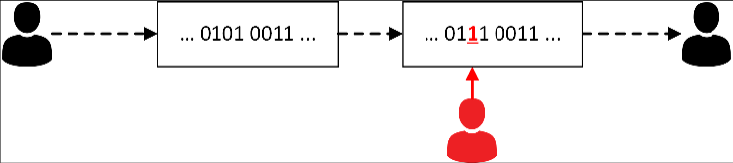
Man In The Middle (MITM) are common attacks that allow attackers to “listen” to communication between two parties. When two hosts communicate with each other, the attacker manages to position himself between them and eavesdrop on this communication.
Different Types of MITM Attacks
Evil-Twin Method
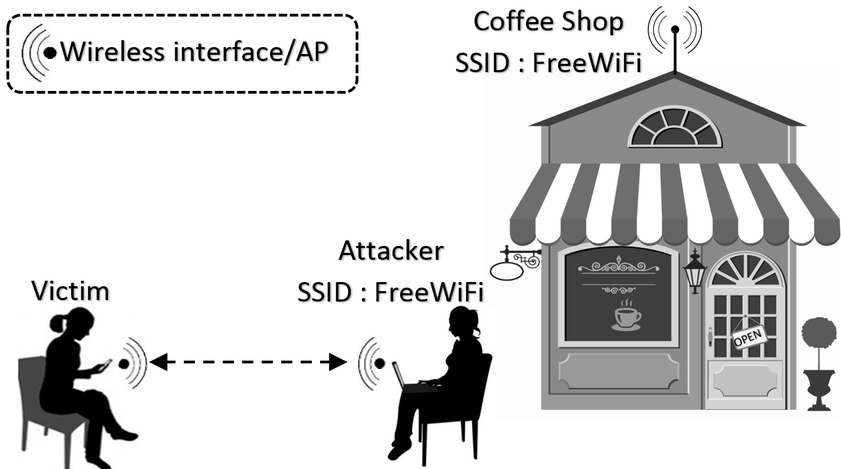
This attack method is nearly two decades old. The way it works is when an attacker broadcasts the same SSIDs as companies, hotels, public WiFis, etc. in order to trick victims’ devices into associating with them. The unsuspected victims which connect to these wireless networks think that they are actually connected to a legitimate and trustworthy provider. The attacker then has their position established between the client device and the internet and is able to read and manipulate traffic for their own gain.
ARP Spoofing/Poisoning
Another common man in the middle attack is ARP Spoofing.
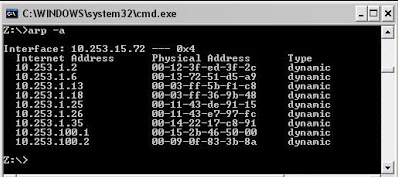
Address Resolution Protocol (ARP) is a protocol that is used for mapping IP addresses to physical machine addresses (MAC addresses).
ARP is a vulnerable protocol that leaves room for attackers to exploit its weaknesses for malicious purposes.
Network hosts will automatically cache any ARP replies they receive, regardless of whether network hosts requested them. Even ARP entries that have not yet expired will be overwritten when a new ARP reply packet is received. There is no method in the ARP protocol by which a host can authenticate the peer from which the packet originated. This behavior is the vulnerability that allows ARP spoofing to occur.
You can see below the arp table of a windows host which has the IP addresses and the corresponding physical address stored into it.
While performing ARP spoofing the attacker can forge ARP packets and send them to
Common tools used for an ARP Spoofing attacks are ettercap and wireshark (for traffic analysis)
Here is a guide to ARP spoofing and poisoning using open source tools. Use it for educational purposes only.
DNS Spoofing
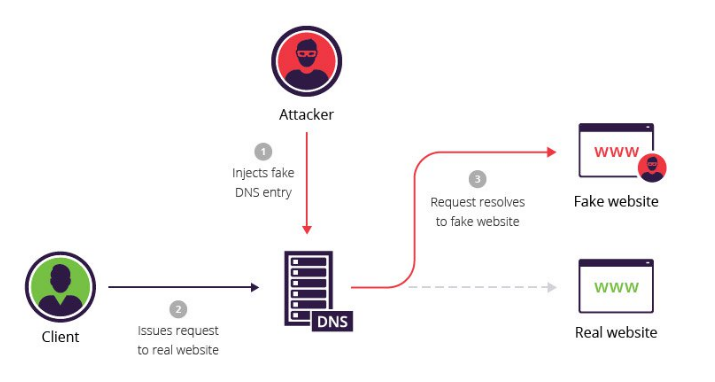
This type of attack is also known as DNS cache poisoning. During this attack altered DNS records are used to redirect online traffic to websites which resemble the legitimate website the user is trying to access.
How An Attacker Can Use MITM Attacks
Packet Sniffing
When the attacker has established himself as a MITM, he can analyze packets on the network and could be able to read sensitive information like usernames, passwords and credit card information. Here is a nice article describing more about packet sniffing.
Packet Injection
The packet injection process allows the attacker to intercept and inject malicious packets in data communication streams.
An example of this is sending a deauthentication message from an unknown party outside the network to a connected client as if it was sent by the wireless router. Check here for a nice tutorial from Null Byte.
Session Hijack
Session hijacking is an extension of sniffing except that sniffing is passive and hijacking requires active participation. The attack consists of the exploitation of the web session control mechanism which is managed for a session token.
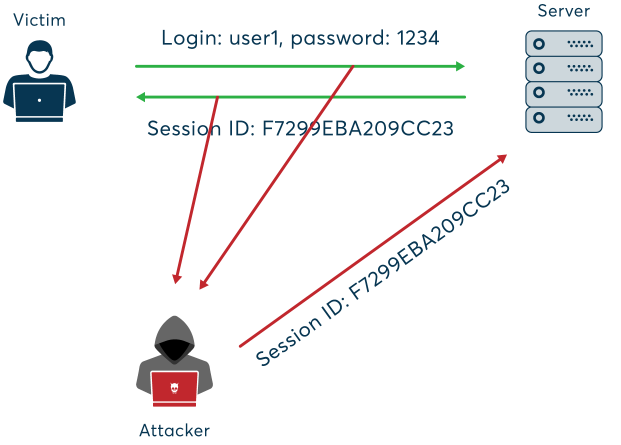
For example, the time between you first log into your bank account, and then log off after your operation, is a session.
During a session hijacking, a malicious hacker places himself in between your computer and the website’s server (Facebook for instance), while you are engaged in an active session.
At this point, the malicious hacker actively monitors everything that happens on your account, and can even kick you out and take control of it.
The biggest advantage of a session hijacking is that the malicious attacker can enter the server and access its information without having to hack a registered account.
Check this link for a session hijack tutorial from Null Byte.
SSL Strip
In order to “strip” the SSL, an attacker intervenes in the redirection of the HTTP to the secure HTTPS protocol and intercepts a request from the user to the server. The attacker will then continue to establish an HTTPS connection between himself and the server, and an unsecured HTTP connection with the user, acting as a “bridge” between them.
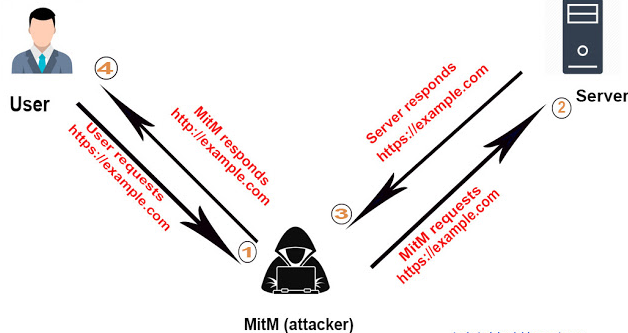
After the successful implementation of an SSL strip attack, the victim’s information is transferred in plain text format and can be easily intercepted by anyone, including the attacker. You may want to check this medium article for a tutorial on SSLStrip.
How to Defend Against MITM Attacks
- Make sure that the DNS servers (DNS caches) that you use are secure. Check the configuration on your router (DNS cache addresses are usually provided via DHCP). If in doubt, use Google public DNS: 8.8.8.8 and 8.8.4.4.
- Limit your sensitive activity on public networks or use a VPN connection on public networks. A VPN will add an extra layer of security.
- Only visit HTTPS websites
- Keep your operating system and your browser always up to date. This way, the attackers will not be able to use exploits to install malware on your computer.
- Create separate wifi networks for guests, internal use, and business application data transfers.
- Install an intrusion detection system (IDS) to monitor your network and alert you to unusual events like attempts to hijack traffic flow.
- Regularly audit and monitor your networks to maintain awareness of normal and unusual activities.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.





