
Google announced the public preview of a tool which helps identify threats within virtual machines running on its Google Cloud infrastructure.
VMTD to Help Identify Crypto Mining
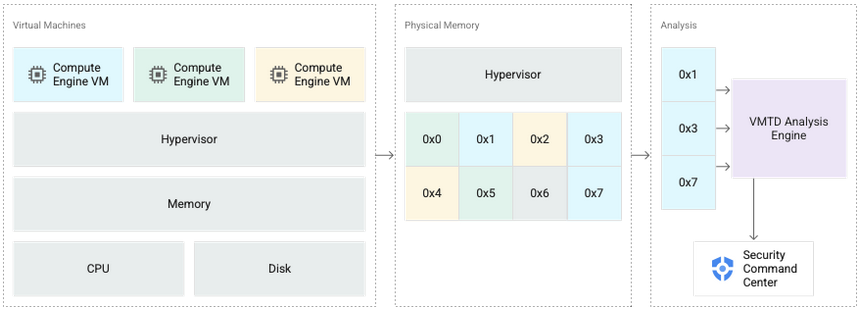
The new Virtual Machine Threat Detection (VMTD), now available in the Security Command Center (SCC), provides agentless memory scanning to help identify cryptocurrency-mining malware and other threats in VMs.
VM Threat Detection is a managed service that scans enabled Compute Engine projects and VM instances to detect unwanted applications running inside VMs. When you enable this service on a resource (an organization or project), scans are automatically configured and scheduled for that resource.
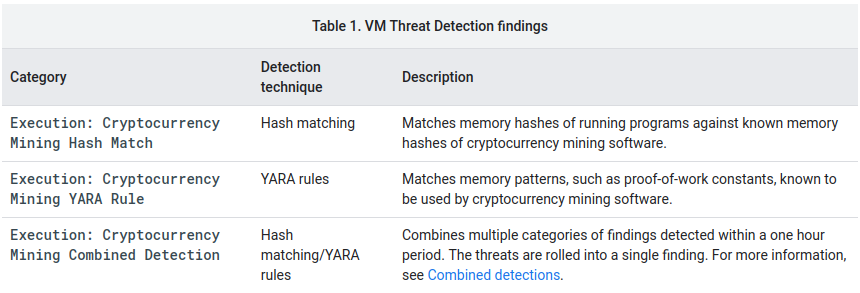
For the Preview, VM Threat Detection includes the following three cryptocurrency mining detections:
No Special Configuration Required
Because VM Threat Detection operates from outside the guest VM instance, the service does not require guest agents or special configuration of the guest OS, and it is resistant to countermeasures used by sophisticated malware.
The main idea behind VMTD is to help customers identify potentially malicious behavior inside their VMs without requiring them to run additional software, thus ensuring that performance is not altered in any way and that the attack surface remains low.
Google Enhancing Security Operations and Threat Response
The launch of VMTD follows other major expansions of security capabilities by Google Cloud, including Cloud IDS, which went into general availability in December. The cloud-native network security offering aims to provide simplified deployment and use compared to existing options.
Meanwhile, Google announced the acquisition of Siemplify to bolster security operations and enhance threat response for customers of Google Cloud.
A recent survey of cloud engineering professionals found that 36% of organizations suffered a serious cloud security data leak or a breach in the past 12 months. And 64% said they expect the problem to get worse or remain the same over the next year, according to the report from Fugue and Sonatype.
Google Cloud’s aim is to make security invisible, to automatically provide a lot of good hygiene under the cover, and only tell you things that you need to pay attention to.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.






