Russian tech company Yandex said that it suffered from the largest DDoS attack ever recorded in the history of the internet.

What is a DDoS Attack?
A DDoS attack, or Distributed Denial of Service attack attempts to disrupt the traffic of the targeted network or server by overwhelming the target with traffic making it unable to operate.
Who Was Responsible?
A botnet called “Meris” is believed to be responsible for this attack, flooding Yandex with millions of HTTP requests for webpages at the same time. A new botnet consisting of an estimated 250,000 malware-infected devices has been behind some of the biggest DDoS attacks over the summer.
The group behind the botnet typically sends menacing emails to large companies asking for a ransom payment. The emails, which target companies with extensive online infrastructure and which can’t afford any downtime, contain threats to take down crucial servers if the group is not paid a certain amount of cryptocurrency by a deadline.
If victims don’t pay, the hackers unleash their botnet in smaller attacks at the beginning that substantially grow in size with time in order to put pressure on the victims.
A Record Breaking Attack
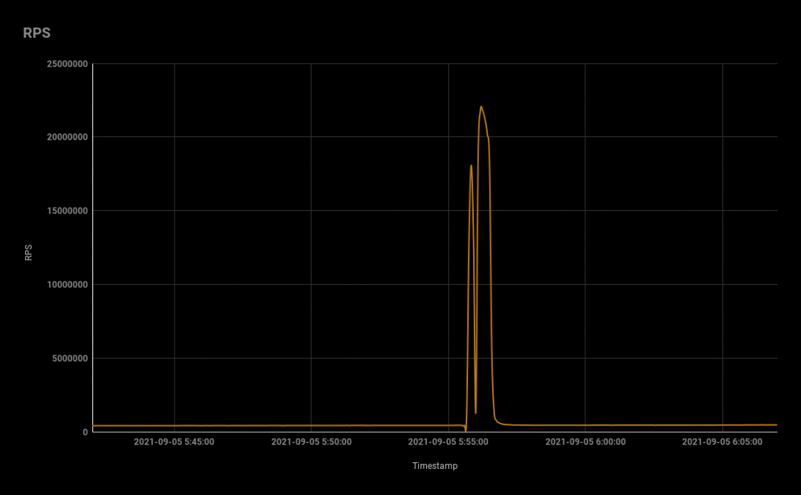
Peaking at 21.8 million requests per second, this attack left the attack reported by Cloudflare on August 19 with 17.2 million requests per second second in the history of DDoS attacks.
Qrator Labs said Meris outdid itself again during an attack that took place this Sunday, September 5.
Botnet mostly consists of compromised MikroTik devices
Qrator says that after analyzing the source of most of the attack traffic, most of it led back to devices from MikroTik, a small Latvian company that sells networking gear such as routers, IoT gateways, WiFi access points, switches, and mobile network equipment.
The company said it wasn’t able to determine if the attacker found and weaponized a zero-day in MikroTik’s software or if they’re just living past exploits.
Nonetheless, a zero-day appears to be in play, just by the large number of MikroTik devices that appear to have been enslaved in Mesir’s gigantic 250,000-strong mesh.
To deploy an attack, the researchers say that Mēris relies on the SOCKS4 proxy at the compromised device, uses the HTTP pipelining DDoS technique, and port 5678.
Mikrotik told Russian publication Vedomosti that it is not aware of a new vulnerability to compromise its products.
The network equipment maker also said that many of its devices continue to run old firmware, vulnerable to a massively exploited security issue tracked as CVE-2018-14847 and patched in April 2018.
However, the range of RouterOS versions that Yandex and Qrator Labs observed in attacks from Mēris botnet varies greatly and includes devices running newer firmware versions, such as the current stable one (6.48.4) and its predecessor, 6.48.3.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.