
A little-known PowerPoint add-on, the .ppam file, has been used by hackers to hide and deliver malicious files.
Security researchers from Avanan, observed that .ppam files were used by attackers to wrap executable files that allow them to take over the target user’s computer.
Attack Method
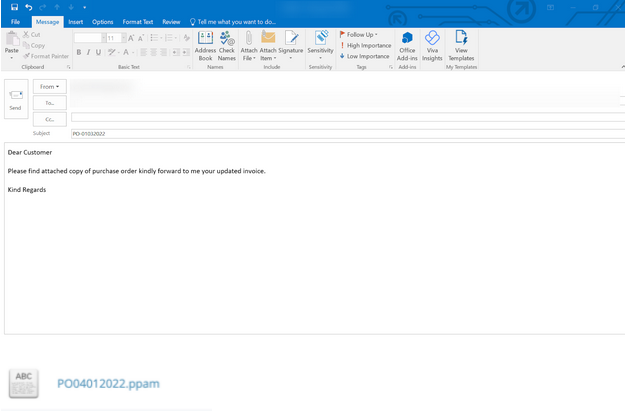
Hackers use emai to deliver their malicious files which can rewrite Windows registry settings.
In this email which tries to trick the user looking like a purchase order has a .ppam file attached which carries the wrapped malicious process in it.
Checkpoint Snandblast analysis shows that the file is malicious:
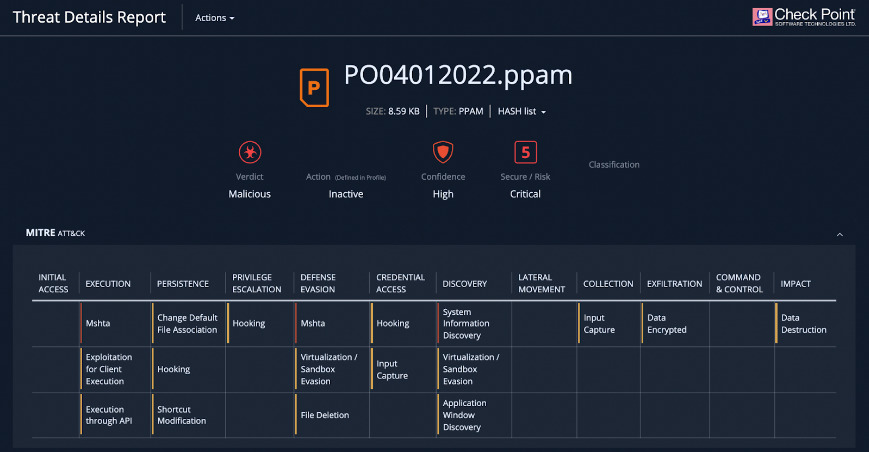
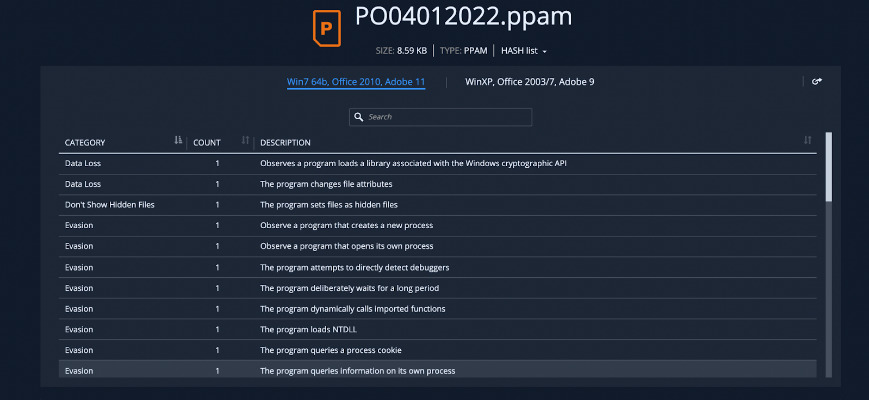
The payload executed a number of functions on the end user’s machine that were not authorized by the user, including installing new programs that create and open new processes, changing file attributes, and dynamically calling imported functions.
Best Practices for Protection
Install email protection that downloads all files into a sandbox and to inspect them for malicious content.
Implement security that can dynamically analyze emails for Indicators of Compromise (IoC). This email failed an SPF check and there was an insignificant historical reputation with the sender
Encourage end-users to reach out to IT when seeing an unfamiliar file.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.





