
What is Nikto
Nikto is an open source scanner capable of scanning for over 6700 items to detect any misconfigurations on web servers like Apache, Nginx, Litespeed etc. as well as discovery of exposed files, user enumeration and outdated components.
Nikto is built into Kali Linux but you may also download it here if you are using another OS.
Nikto Features
- Full HTTP proxy support
- Checks for outdated server components
- Save reports in plain text, XML, HTML, CSV, JSON, NBE, SQL, etc.
- Apache and cgiwrap username enumeration
- Identifies installed software via headers, favicons, and files
- Scan multiple ports on a server, or multiple servers via input file (including Nmap output)
- Host authentication with Basic and NTLM
- Subdomain guessing
- Reports “unusual” headers seen
- Auto-pause at a specified time
- SSL Support
- Enhanced false positive reduction via multiple methods: headers, content hashing, and page content
Easily Get and Run Nikto!
IMPORTANT NOTE:
This tool generates a lot of requests against the target.
Never run this tool against a server without the acknowledgement of the owner.
Remember that if you are performing a penetration test you will need to agree on the scope and methods of the test like discussed in Penetration Testing: Pre-Engagement Interactions
Download from github and run nikto against your target, using the -host flag:
git clone https://github.com/sullo/nikto
# Main script is in program/
cd nikto/program
# Run using the shebang interpreter
./nikto.pl -h http://www.example.com
# Run using perl (if you forget to chmod)
perl nikto.pl -h http://www.example.comIf there are any vulnerabilities or other findings on your target, you will see results similar to these:
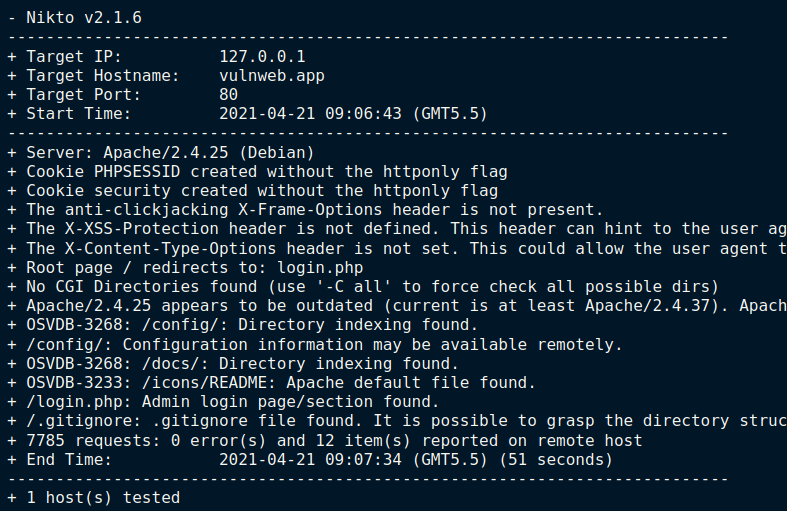
You may use the -output flag to save the result to a file and the -format flag to store the results as HTML,CSV, XML, JSON etc.
./nikto.pl -host http://www.example.com/ -output nikto_output.html -format CSVHow to Scan Multiple Targets From a Text File
To scan multiple IP addresses or domains, just put them in a text file separated by newlines. Nikto will know that the scan has to be performed on each domain / IP address.
nikto -h targets.txtHappy hunting.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.






