According to cyber security researchers from Trend Micro, state-financed Chinese hackers have launched a spear phishing campaign to launch bespoke malware stored within Google Drive to international government, academic, and research organizations.

The Earth Preta APT Group
APT group Earth Preta (aka Mustang Panda and Bronze President) has launched a new wave of large-scale spear-phishing campaigns. Its targets are multiple sectors worldwide using several malware families, including TONEINS, TONESHELL, and PUBLOAD.
Earth Preta is a cyberespionage group known to develop their own loaders in combination with existing tools like PlugX and Cobalt Strike for compromise.
Recent research papers show that it is constantly updating its toolsets and indicate that it is further expanding its capabilities.
How The Attack Works
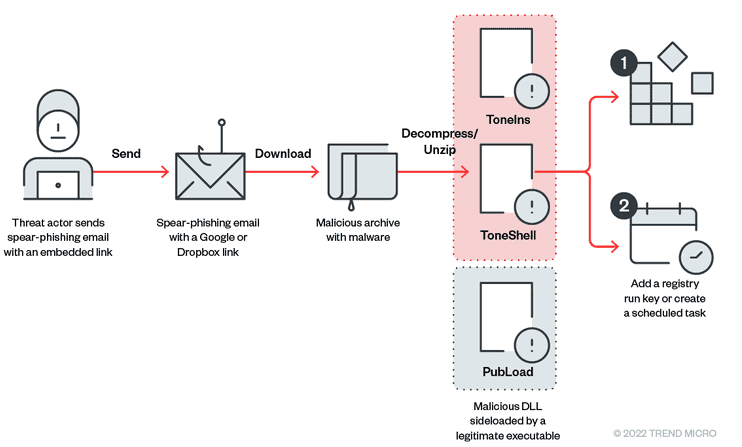
- Earth Preta abused fake Google accounts to distribute the malware via spear-phishing emails, initially stored in an archive file (such as rar/zip/jar) and distributed through Google Drive links.
- Users are then lured into downloading and triggering the malware to execute, TONEINS, TONESHELL, and PUBLOAD. PUBLOAD has been previously reported, but it is tied to TONEINS and TONESHELL, newly discovered malware families used by the group for its campaigns.
- The actors use code obfuscation and custom exception handlers and other techniques to evade detection and analysis.
The Spear-Phishing Emails
The researchers analyzed the contents of the phishing emails and observed that a Google Drive link is used as a lure for victims.
The email’s subject might be empty or might have the same name as the malicious archive.
“Rather than add the victims’ addresses to the email’s ‘To’ header, the threat actors used fake emails.
Meanwhile, the real victims’ addresses were written in the ‘CC’ header, likely to evade security analysis and slow down investigations. Using open-source intelligence (OSINT) tool GHunt to probe those Gmail addresses in the ‘To’ section, we found these fake accounts with little information in them.” the security researchers added.
About The Malware
- First disclosed in May, PUBLOAD is a stager that can download the next-stage payload from its C2 server. Embedded with debug strings, PUBLOAD is capable of distracting analysts from the main infection routines.
- TONESHELL is a shellcode loader and a standalone backdoor without any installer capabilities. It is obfuscated to slow down malware analysis and contains anti-sandbox and anti-analysis techniques.
- TONEINS works as the installer for TONESHELL backdoors and it establishes the persistence for TONESHELL malware.
Researchers have found A, B, and C variants of TONESHELL that indicates it is evolving and becoming more capable.
What Happens Next?
Once the group has infiltrated a targeted victim’s systems, the sensitive documents stolen can be abused as the entry vectors for the next wave of intrusions.
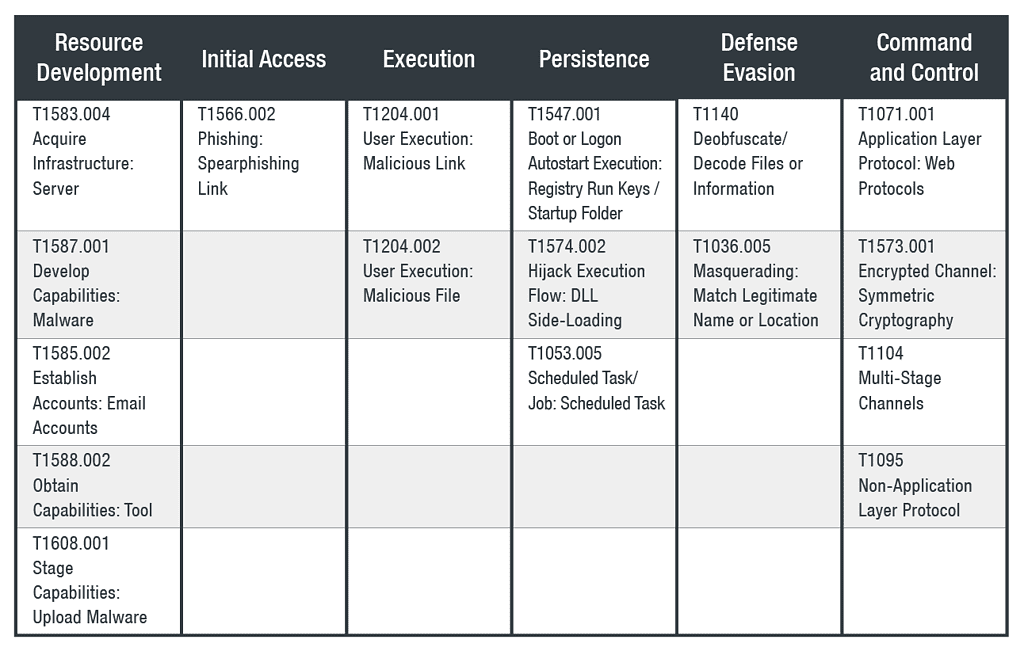
The Attack Described in a MITRE ATT&CK Table
How to Defend Against Earth Preta Attacks
To not be victimized by Earth Preta, Trend Micro recommends companies implement ongoing phishing awareness training for partners and employees. Email recipients should be advised to check the sender and the subject twice before opening an email, especially with an unidentifiable sender or an unknown subject.
Users should also use a multi-layered protection solution to detect and block threats.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.






