Many cyber attacks are carried out by malicious actors with the use of “Botnets”. But what is a botnet?
Botnet is short for “robot-network”. It is a network of malware infected computers that are under the control of the attacker. The attacker is also known as the “bot-herder” and each computer under its control is called a “bot” or “zombie”.
The attacker controls all infected computers centrally and is able to carry out coordinated attacks in large scale.
How Botnets are Built
The simplified stages of building a botnet are:
1. Exposure
During the first phase, attackers find vulnerabilities on websites and applications which can be exploited. They will also try to trick humans through phishing campaigns or online messages to deliver malicious code. The goal is to exploit vulnerabilities in order to deliver malware without the knowledge of the user.
2. Infection
After the target has been successfully exploited the attacker infects it with the botnet malware.
3. Control
During this stage the target computer can be remotely managed by the attacker as part of the botnet network to perform large scale attacks as part of its “zombie network”.
Which Devices are “Candidates” for a Botnet Network

Nearly any computer-based, internet connected device is a potential candidate to become a bot in a botnet. If a vulnerability exists which can allow an attacker to deliver the malware on the device then the device can be hijacked into a botnet.
Some common devices which are candidates for a botnet are:
- Traditional computers/servers
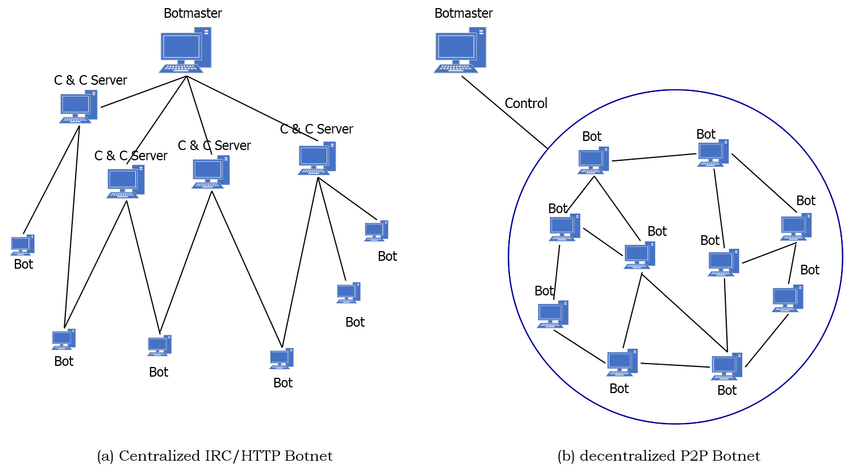
- IoT Devices
- Mobile Devices
- Network Routers
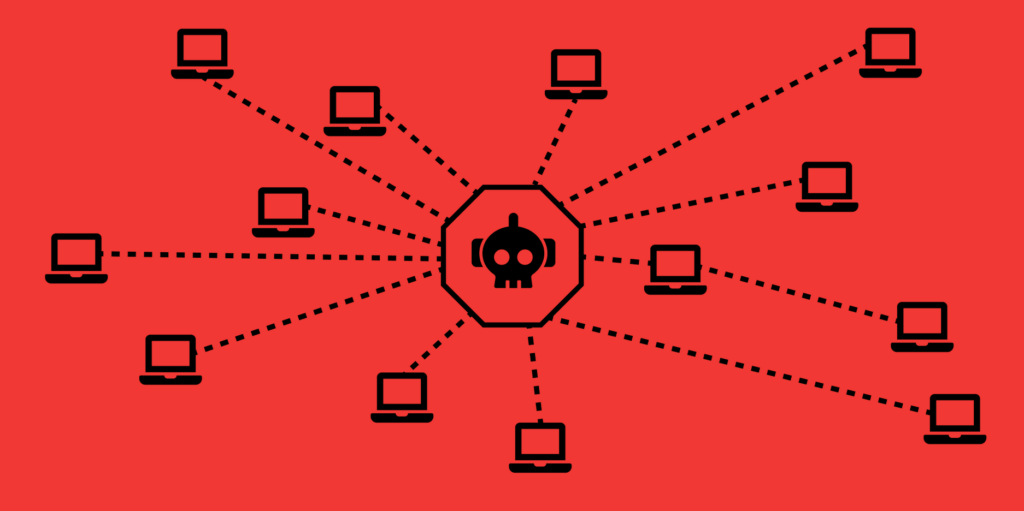
How Botnets Communicate with the Herder
The people controlling the botnets, the herders, can issue commands remotely which is a vital part of the botnet’s operations.
To execute remote commands a central “Command and Control” server is being used to issue instructions to all bots. The commands can be issued either directly or indirectly in the following models:
- Centralized client-server models. In this model commands are issued by one C&C (command and control) server, or through additional sub-herders.
- Decentralized peer-to-peer models. In this model, if the herder can contact any of the infected device, he can spread the commands to other infected devices. This model helps the attacker to conceal his identity and make it hard to be discovered. P2P models are most common today.
Actions Carried out by Botnets
DDoS Attacks
DDoS attacks target organizations for personal or political motives or to extort payment in exchange for ceasing the attack. The attacker leverages the large scale of the botnet to overload a target network or server with requests, rendering it inaccessible to its users.
Email Spam Distribution
Botnets are often being used to send out spam messages, often including malware, to millions or even billions of users. They also use spam emails to spread malware and “recruit” more devices to its network.
Click Fraud
Botnets can also be used to generate fake advertising clicks to increase a site’s revenue or a site’s prominence in search rankings.
Cryptocurrency Mining
Botnets can be instructed to leverage resources (CPU, RAM) on the zombie machines which they are controlling in order to mine cryptocurrencies.
How to Detect Botnets
Botnets are Hard to Detect
There is no general template for what a botnet looks like.
Every botnet is uniquely different in how it is set up, how it grows, and why it exists, which makes it hard to detect. Some botnets are controlled with a central server, others with a peer-to-peer model. The behavior and patterns used on each botnet varies and can be manipulated in a way to evade many detection techniques.
Detection Methods
Signature Based Detection
This approach is used by systems like IDS, where they try to find a signature. The downside is that no new botnets can be
A signature-based Botnet detection technique uses the signatures of current Botnets for its detection. This method has several advantages, such as very low false alarm rate, immediate detection, easier to implement and there is better information about the type of detected attack. Signature based detection method can only able to detect well known botnets.
Thus, unknown Botnets can’t be detected by this method. Anomaly-based detection techniques are introduced to overcome this drawback.
Anomaly Based Detection
The idea behind anomaly-based detection approach is to perform botnet detection by considering several different network traffic anomalies, including high network latency, high traffic volume, traffic on unusual ports, and unusual system behavior that could indicate the presence of malicious bots in the network.
Anomaly-based detection techniques are further divided into host-based detection and network-based detection.
DNS Based Detection
Botnet detection through DNS-based approaches include, detection of failed DNS requests (NXDOMAIN), monitoring of malicious domains, domains with low TTLs and detection of abnormal DNS traffic.
To access the command-and-control server, bots perform DNS queries to locate the particular server that a DDNS (Dynamic DNS) provider typically hosts. It is thus possible to create a detection mechanism that monitors DNS traffic and searches for some DNS anomalies. Botnets frequently use DNS to rally infected hosts, launch attacks and update their codes.
Well Known Botnets
Many botnets have surfaces throughout the years each for their own purpose. Here are some of them.
Mirai
The Mirai botnet was behind a massive distributed denial of service (DDoS) attack that left much of the internet inaccessible on the U.S. east coast. But, what made Mirai most notable was that it was the first major botnet to infect insecure IoT devices. At its peak, the worm infected over 600,000 devices. Most surprising of all: the botnet was created by a group of college kids looking to gain an edge in Minecraft.
Methbot
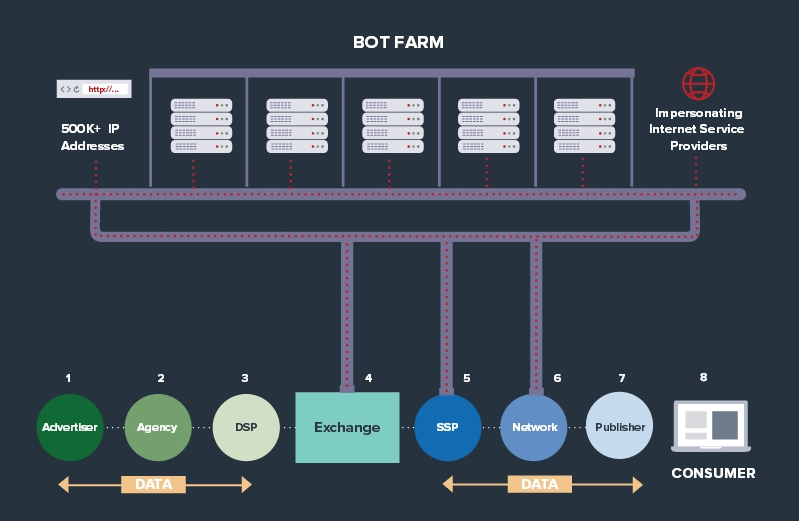
The cyber criminal gang, dubbed AFT13, has developed Methbot robo-browser that spoofs all the necessary interactions needed to initiate, carry out and complete the ad transactions.
To make their bots look more real, the gang is using methods like automated faked clicks, social network login information, and mouse movements.
It was discovered that this botnet had their bot watching as many as 300 million ads per day, with an average payout of $13.04 per 1000 faked views.
Dark Nexus
Dark Nexus is a botnet designed for use in DDoS attacks. It gains access to devices using a combination of default credentials, brute-force attacks, and publicly available exploits. Vulnerable devices are identified using both synchronous and asynchronous scanners, with target IP and port combinations provided by a command and control (C2) server.
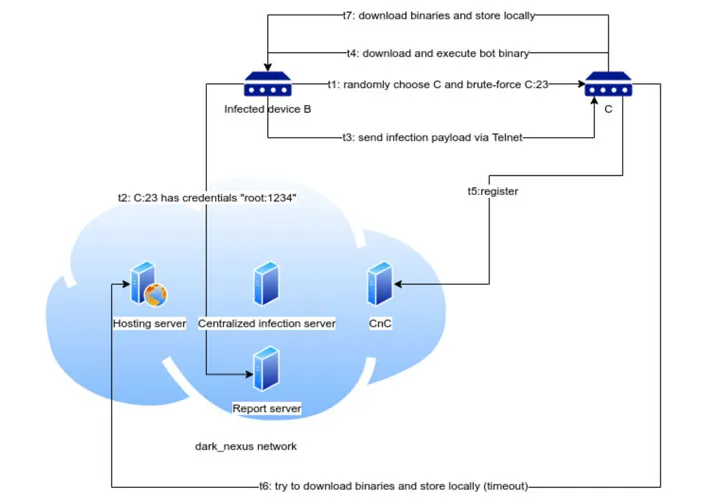
Once It gains access, Dark Nexus will execute shell commands in an attempt to prevent the affected device rebooting, before killing a number of processes. It then connects to a C2 server to download a list of IP addresses to perform DDoS attacks against.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.