The attack surface of your organization can be defined as all the possible entry points an attacker may try to exploit to gain access to systems and information.
Every organization has its own, unique attack surface which needs to be analyzed and defined so that appropriate security controls be designed, implemented and monitored.
Without an attack surface analysis, ad-hoc implementation of security controls will most certainly lead to security gaps which could potentially lead to exploitation by attackers.
“The key to a successfully attacking a network is to know it better than the people who designed it and the people who are securing it. Conversely, the key to defense is to know you own network better than your adversaries.”
Rob Joyce, former chief of Tailored Access Operations, NSA – Usenix Enigma Conference, January 2016
Attack Surface Types
Possible entry points which your attack surface is composed of are: software, servers and client endpoints, web applications, IoT and OT devices but also physical entry points, to your building or your data center. Don’t forget that your employees are also part of the attack surface a malicious actor may try to exploit using social engineering to gain access to systems and company information.
So, summarizing, the attack surface types can be:
- Digital (e.g servers, clients, software, web applications)
- Physical (e.g. doors, windows, locks, physical access to a device)
- Human (e.g. employees)
Relation Between Attack Surface and Attack Vectors
The methods an adversary may use to breach your network are the attack vectors.
The adversaries use attack vectors that target weaknesses in your security to compromise your systems and infiltrate your network.
Attack vectors can be unique to your company and may take many forms. Some common attack vectors are:
- Compromised Credentials
- Software Vulnerabilities
- Weak Passwords
- Malicious Employees (malicious insiders)
- Poor encryption
- Ransomware/malware
- Phishing
- Misconfigured devices
- DDoS attacks
- Trust Relationships
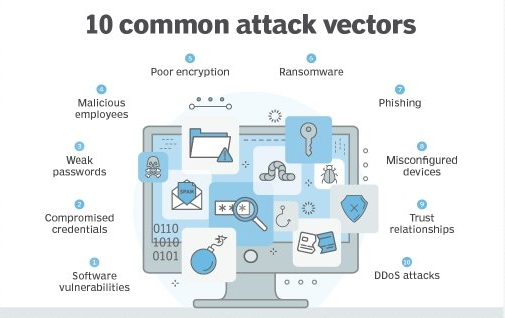
An attacker can use one attack vector to try and compromise a system, but not all attack vectors can be used against all types of assets.
For example, phishing is an attack vector that targets your employees, while DDoS targets your network infrastructure and/or a web application.
Use of Attack Vectors
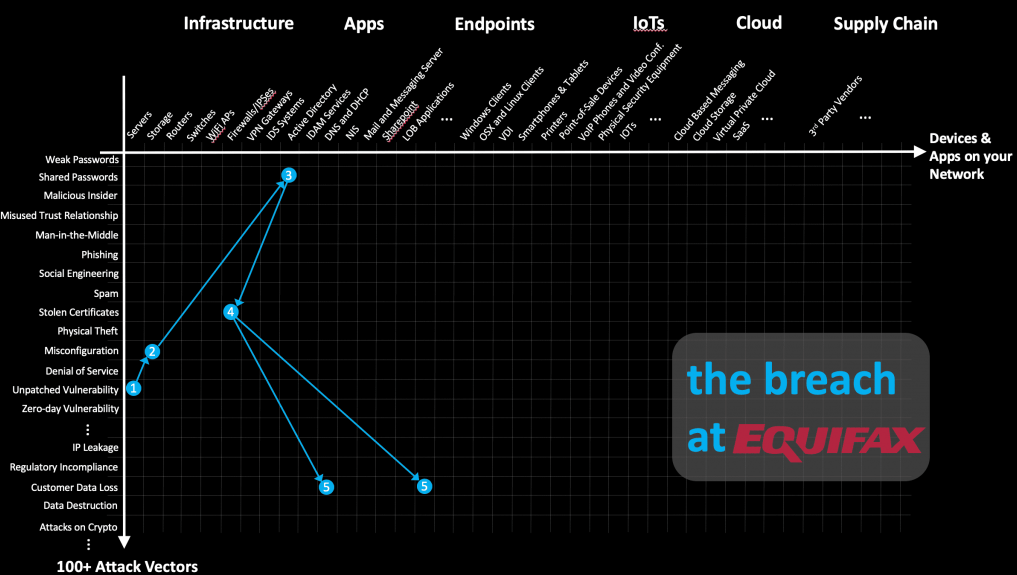
In the below illustration, you can see the lateral movement of the Equifax attackers during the 2017 breach.
The attacker’s initial attack vector (1) was an unpatched vulnerability on a publicly facing server.
Compromising this server broadened the attack surface, allowing the attacker access to the internal network of the company.
Internal and External Attack Surface
There are two types of attack surfaces: internal and external.
External attack surface will include externally facing systems and applications, cloud-based or On-premise hosted, and other third-party assets.
Following the example above, it is essential to note that when mapping your company’s attack surface, or designing your security controls, focus first on your high-risk assets like your externally facing systems and applications, but do not neglect to apply a defense-in-depth strategy, covering your internal attack surface.
Internal attack surface analysis aims to block insider threats like hijacked accounts. An insider threat could derive from a disgruntled employee or a worker that has been duped into actions through phishing.
Attack Surface Management
Attack surface management can be challenging even for small organizations. New assets are continuously created especially with the increasing use of the cloud and virtualization technologies, which make the creation of new networks and servers easy and quick.
Achieving complete visibility and monitoring to reduce risk exposure is a hard task both for small and large teams.
Attach surface management encompasses many activities by which you discover your assets, classify them according to their criticality, prioritize their protection with appropriate security controls and apply continuous monitoring of them.
Attack Surface Analysis and Mapping
This process typically involves a thorough examination of the system’s architecture, configurations, and dependencies to identify any vulnerabilities or weak points that an attacker could exploit.
To perform attack surface analysis and mapping, you can follow these steps:
- Identify the scope of the analysis. This typically involves defining the boundaries of the system or network that you want to examine, as well as any specific components or services that you want to focus on.
- Conduct a thorough examination of the system’s architecture, configurations, and dependencies. This may involve reviewing documentation, interviewing stakeholders, and using tools to scan the system for vulnerabilities. Do not forget to map the software used on your machines.
Log4j vulnerability showed the world how little visibility IT teams have on their infrastructures.
- Identify potential attack vectors. As you examine the system, look for any potential points of entry that an attacker could use to gain access, such as open ports, unpatched software, or misconfigured services.
- Map out the attack surface. Once you have identified all the potential attack vectors, create a visual representation of the attack surface, showing the relationships between different components and potential entry points.
- Identify and prioritize vulnerabilities. Use the information gathered during the analysis to identify and prioritize the vulnerabilities that pose the greatest risk to the system. This may involve assessing the likelihood and impact of each vulnerability, as well as the feasibility of exploiting it.
The information you have collected during these stages will aid in the attack surface reduction.
Attack Surface Reduction
It is often advisable to reduce your attack surface, when possible. Having fewer entry points to protect and control will also reduce the probability of their exploitation. It will also allow your team to focus on strengthening the security of those entry points.
As general advice towards the reduction of your attack surface, you should first develop and implement a plan to mitigate the identified vulnerabilities.
Then you must engage with your team(s) (developers, IT, business units) to take further steps to remove or disable unnecessary systems, components, and services to prevent unauthorized access to them or future malicious actions from attackers who will continuously monitor your assets for emerging vulnerabilities.
Attack Surface Monitoring
Attack surface monitoring is the security practice of monitoring your information assets to look for entry points the attackers may use to try and access your network and your data.
- Implement monitoring tools and processes and establish baseline configurations to have a reference point against which you can compare future changes or modifications, and this will help you to identify any potential vulnerabilities or deviations from the norm.
- Regularly scan your systems and networks for changes or anomalies that could indicate a potential vulnerability or attack. When you identify such changes, investigate them further and take appropriate action to mitigate the risk.
- To ensure that your attack surface monitoring efforts are effective, you will need to regularly update and maintain your monitoring tools and processes. This may involve installing updates, fine-tuning settings, and incorporating new technologies or techniques as they become available.
Conclusion
Analyzing and understanding your attack surface is not an easy task. Shadow IT often complicates your efforts on protecting your information assets. IT devices and tools used within the organization without the knowledge and approval of the IT and Security departments are not properly protected since they are not
You cannot protect what you don’t know, or understand. Knowing your organization’s attack surface is the first and essential step to protecting your information assets efficiently and effectively.
It’s important to note that attack surface management is an ongoing process, as systems, networks, software, and other components are constantly changing. As such, it’s important to regularly review and update your efforts to ensure that they remain effective in detecting potential vulnerabilities and attacks.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.