Continuous integration (CI) and continuous delivery (CD), also known as CI/CD, embody a culture, operating principles, and a set of practices that application development teams use to deliver code changes more frequently and reliably.
CI/CD is a best practice for DevOps teams. It is also a best practice in agile methodology. By automating integration and delivery, CI/CD lets software development teams focus on meeting business requirements while ensuring code quality and software security.
Attackers Are Targeting CI/DC
Hackers are moving their focus to attack CI/CD because they have realized that CI/CD services offer an effective way to accessing an organization’s most valuable assets.
Security risks of CI/CD pipelines include:
- Insecure Code.
- Poisoned Pipeline Execution (PPE)
- Insufficient PBAC (Pipeline-Based Access Controls)
- Insecure System Configuration.
- Usage of Third Party Services.
- Supply Chain Attacks.
- Exposure of Secrets.
Rise of Security Incidents of the CI/CD
The industry is witnessing a significant rise in the amount, frequency and magnitude of incidents and attack vectors focusing on abusing flaws in the CI/CD ecosystem, including:
- The compromise of the SolarWinds build system was used to spread malware through to 18,000 customers.
- The Codecov breach led to the exfiltration of secrets stored within environment variables in thousands of build pipelines across numerous enterprises.
- The PHP breach resulted in the publication of a malicious version of PHP containing a backdoor.
- The Dependency Confusion flaw, which affected dozens of giant enterprises, abuses flaws in the way external dependencies are fetched to run malicious code on developer workstations and build environments.
- The compromises of the ua-parser-js, coa and rc NPM packages, with millions of weekly downloads each, resulted in malicious code running on millions of build environments and developer workstations.
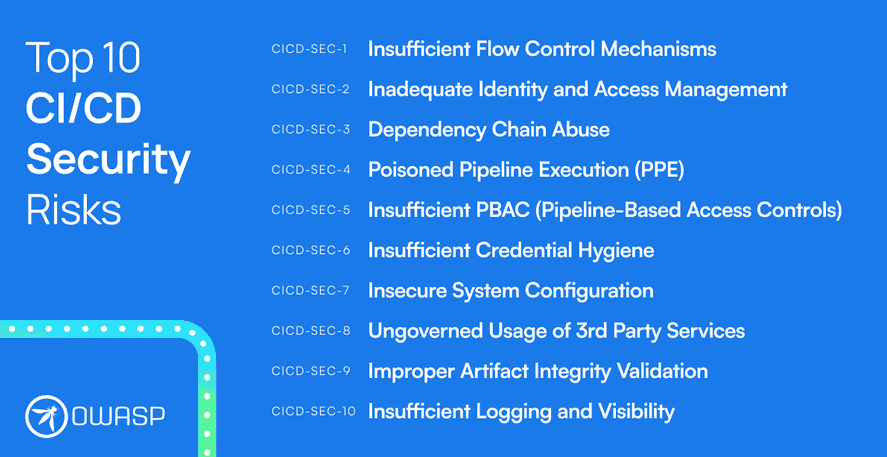
What is the OWASP “Top 10 CI/CD Security Risks” initiative
The “Top 10 CI/CD Security Risks” initiative brought numerous industry experts across multiple verticals and disciplines came together to collaborate and produce a document to ensure its relevance to today’s threat landscape, risk surface, and the challenges that defenders face in dealing with these risks.
This project guides defenders through the process of identifying target areas for the purpose of safeguarding their CI/CD ecosystem. It is the product of considerable study into attack vectors linked with CI/CD, as well as the investigation of high-profile breaches and security weaknesses in existing systems.
The Top CI/CD security risks
The list was compiled on the basis of extensive research and analysis based on the following sources:
- Analysis of the architecture, design and security posture of hundreds of CI/CD environments across multiple verticals and industries.
- Profound discussions with industry experts.
- Publications detailing incidents and security flaws within the CI/CD security domain. Examples are provided where relevant.
The Top CI/CD security risks:
CICD-SEC-1: Insufficient Flow Control Mechanisms
CICD-SEC-2: Inadequate Identity and Access Management
CICD-SEC-3: Dependency Chain Abuse
CICD-SEC-4: Poisoned Pipeline Execution (PPE)
CICD-SEC-5: Insufficient PBAC (Pipeline-Based Access Controls)
CICD-SEC-6: Insufficient Credential Hygiene
CICD-SEC-7: Insecure System Configuration
CICD-SEC-8: Ungoverned Usage of 3rd Party Services
CICD-SEC-9: Improper Artifact Integrity Validation
CICD-SEC-10: Insufficient Logging and Visibility
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.






