
WHAT IS IT
Fileless malware is an advanced threat that can use legitimate software to compromise systems to steal information, leaving no trace to perform forensic analysis to find the root cause.
Hackers utilize fileless malware by injecting malicious code, scripts, or libraries into documents and web pages. This code is referred to as LOLBins, or living-off-the-land binaries.
LOLBins utilize whitelisted, legitimate software applications that exist on the targeted device, but use them with malicious intent. Commonly abused tools include PowerShell, PsExec, or Windows Management Instrumentation (WMI).
TYPES OF FILELESS MALWARE
Document Based
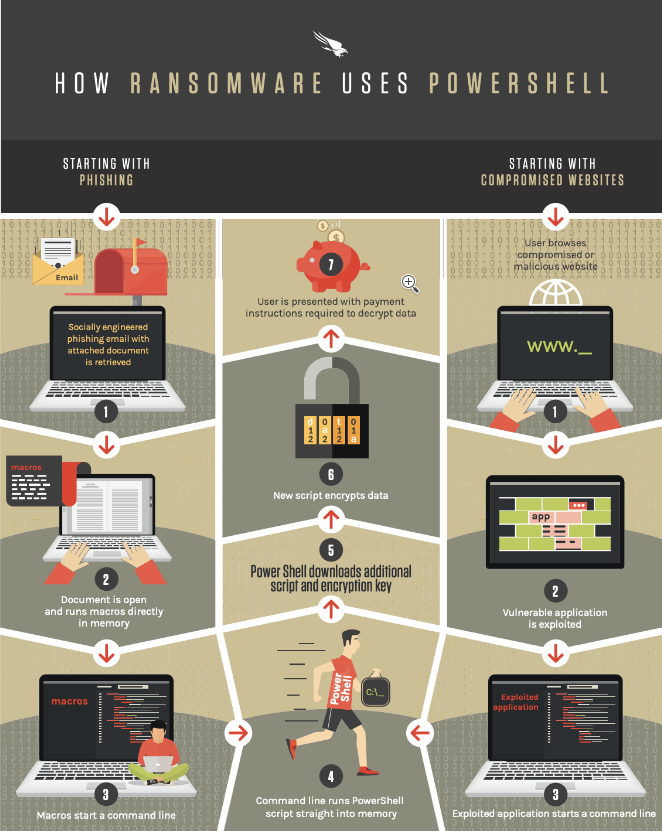
Malicious documents with macros can be used to run Powershell and automate other actions like the download of malicious payloads or run other legitimate commands to facilitate data exfiltration.
Web Based
Such attacks can utilize scripting languages which can be executed on a web page, like Javascript which is heavily used by most websites. In this case the javascript executes on page load and can be used to run powershell on the target system, initiating further actions for malicious purposes.
INCREASE OF ATTACKS
In 2019 there has been a 265% increase of such attacks compared to 2018 according to Trend Micro’s 2019 Midyear Security Roundup.
TRADDITIONAL DEFENSE METHODS ALONE WILL NOT WORK
There are several challenges in dealing with fileless attacks with only traditional AV and Firewalls:
- Fileless attacks never create a file, which makes file-based detection methods completely ineffective.
- Fileless techniques were common in targeted attacks and as the first stage of malware infection from a browser – but now the entire attack can be fileless.
- Fileless attacks often pivot from memory exploits to PowerShell code (which is not inspected by most EPP solutions). These white-listed apps typically have full control to replicate and remove fileless components and move to legitimate access.
- Patch processes aren’t fast enough to keep up with browser or app patches.
HOW TO DEFEND
- Have your computers and servers patched and up to date.
- Have a solid security awareness training policy and culture.
- Understand how your systems work so you can spot anomalies and raise red flags.
- Check your ability to detect PowerShell, cmd scripts running on your systems.
- Remove administrative tools especially when they are not needed, and restrict access to the programs that are allowed to run on systems through Windows Group Policy and/or WindowsAppLocker.
Additionally, Microsoft has developed an open interface called AntiMalware Scan Interface (AMSI) to make it easier to detect and analyze ta scripting behavior on systems/applications.
Dimitris is an Information Technology and Cybersecurity professional with more than 20 years of experience in designing, building and maintaining efficient and secure IT infrastructures.
Among others, he is a certified: CISSP, CISA, CISM, ITIL, COBIT and PRINCE2, but his wide set of knowledge and technical management capabilities go beyond these certifications. He likes acquiring new skills on penetration testing, cloud technologies, virtualization, network security, IoT and many more.






